
Whether your organization operates in healthcare, retail, finance, or any other regulated industry, establishing and maintaining an effective IT compliance program is mandatory.
An IT compliance audit is more than just a box-ticking exercise for regulatory authorities, however. Undertaking regular and comprehensive IT compliance audits significantly strengthens your company’s capacity to protect sensitive information, enhances your organization’s reputation, and streamlines its organizational efficiency. All of these work, ultimately, to boost your bottom line.
What exactly is an IT compliance audit though? Is it really so important? And what exactly does it involve?
We answer these questions to help you on your way to achieving an effective IT compliance program that will benefit your organization and the people you serve.
What is an IT compliance audit?
An IT compliance audit is a systematic review of an organization’s IT infrastructure, operations and policies to determine the effectiveness of its cybersecurity protocols and adherence to relevant regulations.
The exact focus of an IT compliance audit is industry-specific but, in general, it covers a wide range of IT services and policies, including software applications, user access controls, and risk management procedures, among many others.
As with financial audits, an IT compliance audit is a comprehensive and probing process. Rather than seeking to identify financial irregularities, however, the primary goal of an IT compliance audit is to identify potential weaknesses in your organization’s approach to IT that could threaten the integrity of any stored or transmitted data.
With this knowledge, your organization can take preemptive action to mitigate potential risks in an accurate, reliable and timely manner.
Why IT compliance audits are important
IT compliance audits perform three critical functions that serve the best interests of your organization, your employees, and the people you serve.
1. Meet regulatory requirements
The first point on the IT audit compliance checklist is to refer to the industry standards and regulations that apply to your organization concerning handling data.
These regulations fall into one or more of three categories:
General
Such regulations apply to an array of organizations irrespective of their location or industry. One notable IT compliance audit example is the National Institute of Standards and Technology (NIST) Special Publication 800-53 which details the standards of security and privacy controls for information systems and organizations.
Regional
These regulations only apply in particular countries, regions (such as the EU), or US states so are not relevant if you don’t operate there. Some IT compliance audit examples include the EU General Data Protection Regulation (GDPR), the UK Data Protection Act, and the New York State Department of Financial Services (NYDFS) Cybersecurity Regulation.
Industry
Such regulations only apply to organizations in specific industries or ancillary organizations that handle certain types of data. Some IT compliance audit examples include the Health Insurance Portability and Accountability Act (HIPAA) for healthcare providers and the Payment Card Industry Data Security Standard (PCI DSS) for financial services companies.
Failure to comply with any of these could incur hefty fines and legal fees. Moreover, new regulations and amendments are frequently adopted so maintaining IT compliance is an ongoing process requiring periodic reviews.
2. Risk identification and mitigation
With so much sensitive information stored digitally, we rely on cybersecurity systems to protect the integrity of our data. In their absence, personal information and intellectual property are vulnerable to leaks, loss, and theft.
IT compliance audits are all about putting the effectiveness of these security systems to the test.
This means carrying out assessments such as disaster recovery tests and penetration (PEN) tests to identify potential vulnerabilities in your organization’s IT framework that could facilitate data leaks or theft and then putting measures in place to address them before they become a serious problem.
As with regulatory compliance, this is an ongoing process. New vulnerabilities can emerge unexpectedly and cybercriminals are constantly developing new strategies to infiltrate IT networks.
3. Organizational efficiency
Another important aspect of IT compliance audits is that they present an opportunity to boost the efficiency of your organization.
On top of minimizing risk exposure, the auditing process also results in action that improves your IT system’s overall reliability, availability and speed, and reduces the amount of time spent investigating and remediating security breaches.
IT compliance audits also provide an opportunity for employees and departments within an organization to collaborate around the shared goal of strengthening the resilience of an IT network and sharpening everyone’s understanding of it. This too often results in more efficient workflows.
Internal vs external IT compliance audits
IT compliance audits can be carried out internally and externally.
An internal IT compliance audit is performed by an in-house individual or team, usually the ones responsible for the organization’s IT security. The purpose is to provide a detailed risk assessment but also to determine whether the organization is meeting its regulatory obligations and whether the organization’s use of IT is helping it meet its overall objectives.
External audits are more formal and are carried out by an independent third party that has either been assigned the role by a regulatory authority or by the organization’s board of directors.
Internal and external compliance audits are not, however, exclusive to one another. Typically, they complement each other, with an internal compliance audit preparing the way for a later external auditor’s investigation.
The primary focus of an external auditor is often to assess whether particular state, federal or corporate regulations and standards are being adhered to. These audits tend to follow a set format depending on the compliance standards under assessment, and they entail the possibility of fines and/or legal action for noncompliance or referral to another body for further investigation.
An external auditor could also, however, be a third party hired by the organization if they cannot carry out an IT compliance audit internally. This is the case for many small and medium-sized businesses and the focus, therefore, is centered on evaluating overall risks to compliance and security.
What is the scope of an IT compliance audit?
All IT compliance audits entail a comprehensive and systematic review of an organization’s IT setup, but the precise scope, understood as the depth and breadth of the audit, can vary substantially.
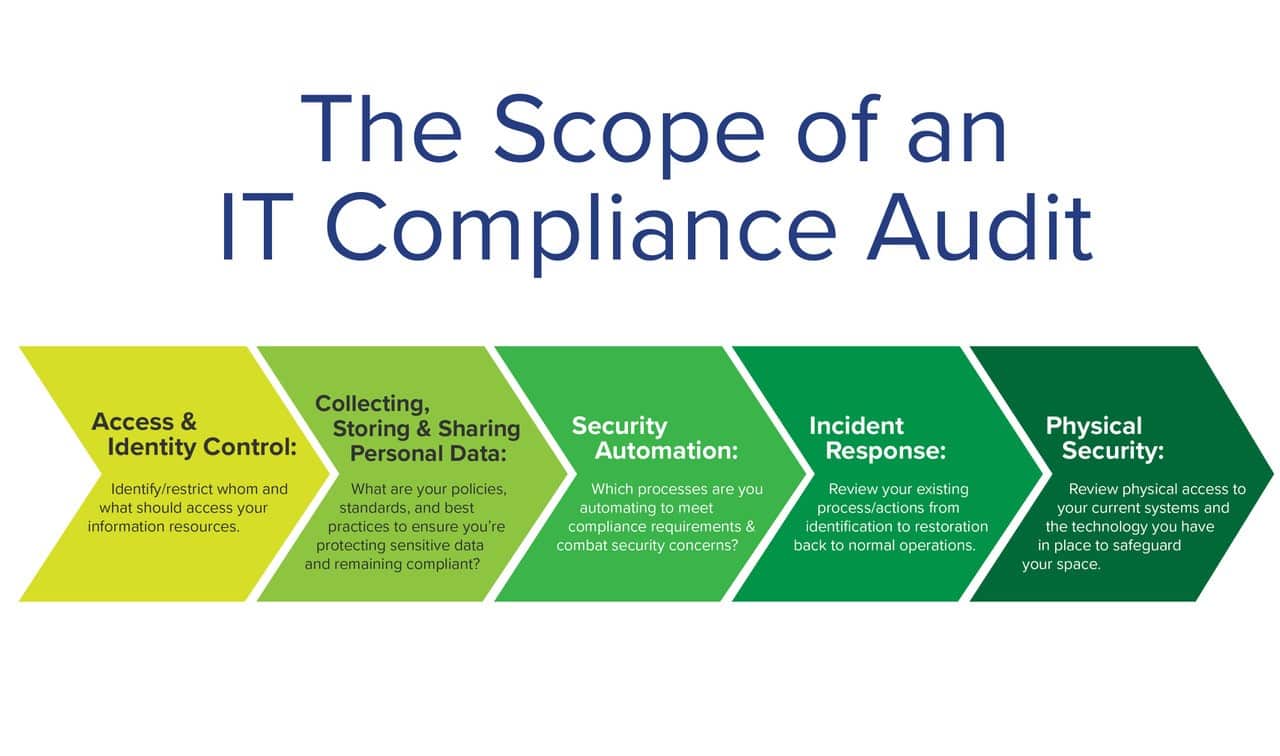
The scope is determined by what the purpose of the audit is in the first place. An internal IT compliance auditor charged with assessing whether the organization’s IT security framework aligns with its broader goals will have different objectives to an external auditor trying to determine whether the organization is upholding the standards of HIPAA.
But, in general, five key areas form an IT compliance audit. These, and some of the questions that an auditor will seek to answer, are as follows:
1. Access and identity control
For instance, is the organization enforcing the Principle of Least Privilege (PoLP)? Is there a system in place to revoke access when it is no longer required? Can inactive user accounts be detected and managed?
2. Collecting, storing and sharing personal data
Is the collection of personal data necessary? Has consent been obtained beforehand? Is your organization respecting the user’s data in terms of how it is accessed and used? Is this data being shared with third parties and, if so, is it necessary and lawful? Are there systems in place to delete personal or sensitive data when it is no longer needed?
3. Security automation
Most security procedures must be automated, which means employing some of the following technologies, which an auditor will review.
- Antivirus and anti-malware programs
- Data discovery and classification tools
- Security Information and Event Management (SIEM) solutions
- Endpoint Detection and Response (EDR)
- Intrusion prevention system (IPS)
4. Incident response
An It compliance audit will assess your organization’s incident response plan (IRP). This comprises the following five steps:
4.1. Preparation
Are security policies in place and are they understood by the employees?
Is it clear what a ‘security incident’ is?
Have responsibilities for each step of the IRP been assigned?
4.2. Detection and analysis
This is the “who, what, where, when, and why” step, followed by an assessment of the impact the incident is likely to have on the organization’s normal operations.
4.3. Containment
Is the incident containable, and how? If it cannot be contained then what mitigation measures can be put in place?
Have the affected and unaffected systems been isolated from one another?
4.4. Eradication and recovery
Are all relevant software updates and patches up to date?
Are there any configuration errors?
Have all possible entry points been reviewed and sealed off?
Are the affected systems now free of malicious activity?
4.5. Post-incident activity
Has each step of the IRP been documented?
Have you scheduled a meeting to discuss the IRP report with employees?
5. Physical security
Is physical access to servers and computers that store sensitive information restricted and under surveillance?
IT compliance audit solutions with Vertikal 6
Vertikal 6 offers complete IT compliance audit solutions for organizations looking to enhance their cybersecurity and remain compliant in an ever-changing regulatory environment.
Our IT compliance services include:
- Penetration testing
- Proactive security and vulnerability assessment
- Security policy management and development
- Gap analysis
- Support with reporting capabilities
- End-user education
To benefit, get in touch with us.
Start here to level up your IT.
Click below or call our Rhode Island headquarters at: 401-825-4400.









